Why your customers can't afford to not be protected
With the increasing adoption of cloud platforms, quite a considerable number of businesses have made the move to the cloud. Whether moving complete processes to the cloud or a hybrid solution, the security architecture that used to be valid for on prem, is no longer a viable solution that can be applied to a cloud model. The increased use of the cloud demands an increased level of security, especially in technologies that secure workloads, containers, and serverless applications on multi- and hybrid-cloud environments.
Hosting providers offer their own security solutions, and this has improved over the years, but is it at the level that this alone is sufficient to protect, assess and mitigate the most advanced threats we’re seeing recently? Most organisations who consider security a pre-requisite, procure solutions from reputable security vendors to protect and continually assess their environments.
Check Point Research has revealed a staggering 168% year on year increase in the number of cyberattacks in the APAC region.
There has been a 13% weekly increase of cyber-attacks on organisations in the APAC region since the beginning of the year, with 1338 weekly attacks per organisation.
Cyber Attacks are becoming more frequent, and they’re becoming considerably more sophisticated than ever before.
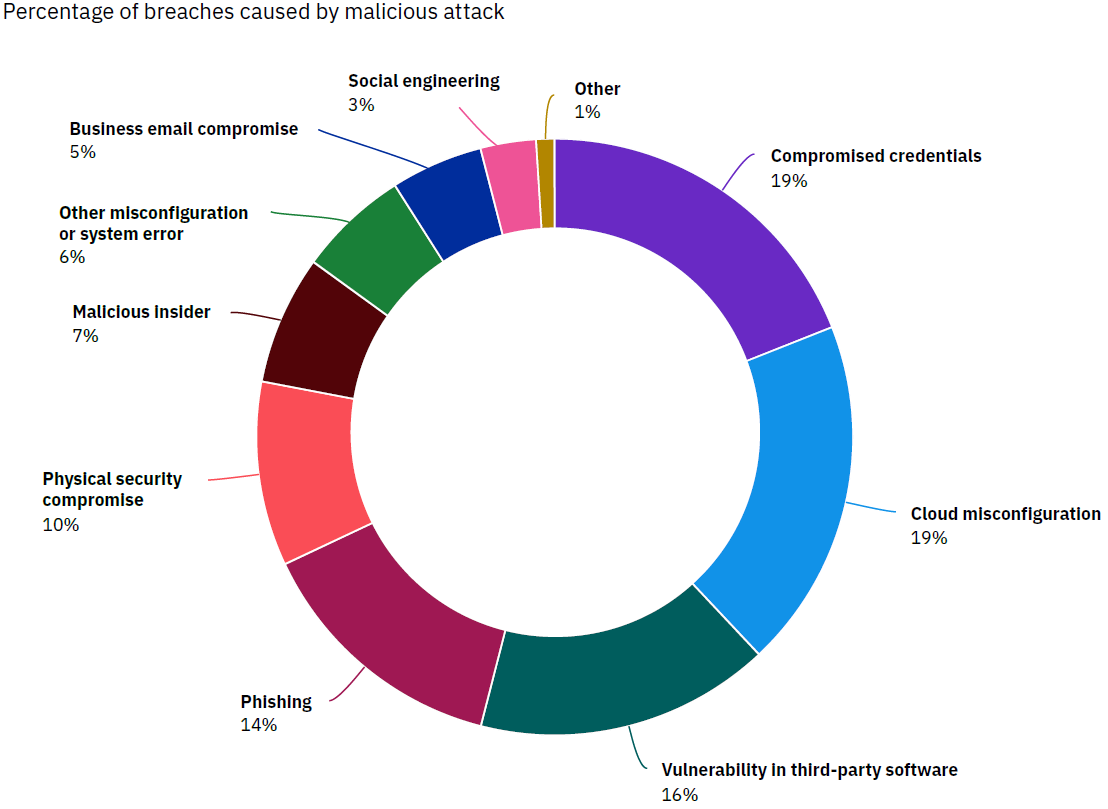
Many vectors are used for threats to attack, but the 2 leading vectors that enable the greatest number of breaches that stand out in cloud platforms are Compromised Accounts and Cloud Misconfigurations, followed by Vulnerabilities.
Cloud Security and Compliance requirements generate a great number of challenges, all which can expose the platform to cyber threats if not attended to. Challenges such as configuration drift, misconfigurations, shared responsibility models, ever changing workloads, and minimal visibility across the platform or platforms is the challenge administrators are facing in this modern world of the cloud.
Recent attacks we’ve all heard about the crippling ransomware that hit JBS meat supplies worldwide. The fuel delivery supply chain in the US crippled by ransomware. Another one that you may not be aware is Channel 9 in Sydney.
Ransomware and other catastrophic threats expose data breaches. In 2020 there were over 30 billion records exposed in data breaches. This was noted as more than the total of the previous 15 years combined.
What can you do to protect your Cloud environment?
A crucial element of cloud security is focused on protecting business assets, whether it’s confidential data, identities, financial records, etc.
- Maintaining a strong cloud security posture will increase protection for organisations from threats.
- Achieving visibility across the platform or platforms, as well as designing the architecture correctly, all contribute to minimising the risk and exposure.
- Understanding which assets have open ports or public facing IP’s, or which storage buckets are open to the public is important and maintaining the best practices across the platform is imperative, as is controlling and protecting lateral movement across the platform.
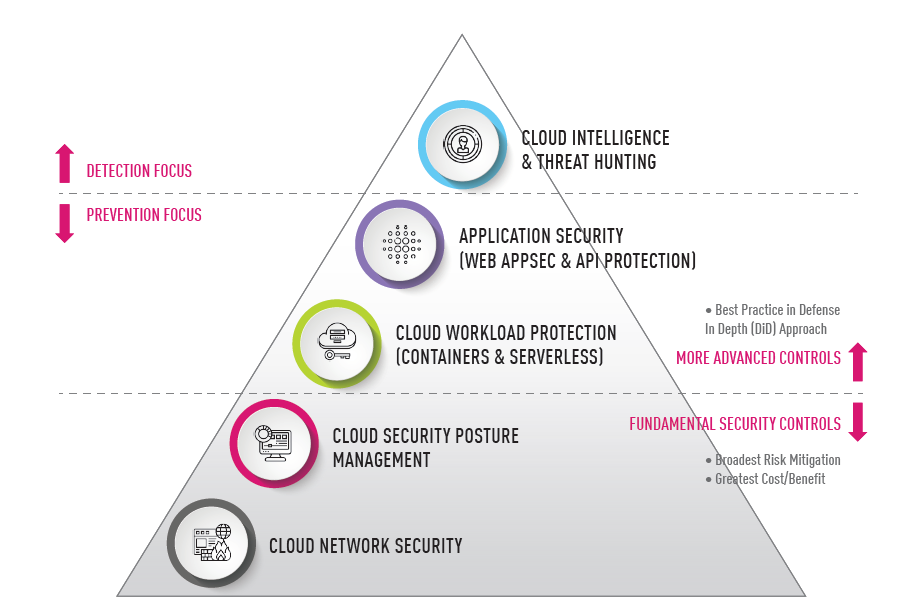
The Figure above illustrates the kind of multilayered, yet unified, cloud security platform that organisations should put in place to protect their cloud deployments and ensure a robust cloud security posture.
There are many products that assist in securing cloud environments using reputable security vendors’ solutions. Administrators are presented with challenges every day to secure cloud platforms. Some of the challenges include Posture Management, zero day threat prevention, vulnerability protection, complete visibility across platforms, data compliance, and many more. Implementing strategies around Risk Assessment, Governance, Business Resilience, and using tools to assist with Identity Awareness, MFA, ZTNA, XDR is becoming the new normal for Cloud platforms.
Below are some best practices to be taken as an action checklist to improve your security posture:
- Active Protection and Prevention against threats, vulnerabilities, identity theft, data loss, and accidental or unauthorized changes.
- Continuous Risk Management and Assessment and enforcement of regulatory compliance standards and security best practices, with auto-remediation.
- Complete visibility into all assets, workloads, and security policies across all networks.
- Clarify responsibilities with your Hosting Provider.
- Implement least privileged access across the network and extending this to a Zero Trust model across local and/or Hybrid solutions.
- Granular IAM controls including MFA solutions.
- Strong threat reporting and threat hunting solutions across the whole platform. A strong focus on XDR, SIEM, and SOAR solutions.
- Defence in Depth across the platform.
Organisations should consider assessing their postures often with Cloud Security Posture Management and approaching the task of strengthening their cloud security postures as an ongoing process.

Meet the Team: Andy Taylor - DAS State Sales Manager

Federal Budget 2026–27: What It Means for SMB Technology Planning, Cybersecurity and Channel Partners

One HPE, One Opportunity: How Dicker Data Is Accelerating Partner Growth in 2026
Partner With Us
Our resellers outperform the competition and deliver next-level solutions for clients thanks to our unique, value-added services.
You May Also Like
These Related Stories

Secure your everything: a guide to layered security

There's a talent shortage in IT Security - here's how you can address it






