SASE. What’s this new buzz word we keep hearing about? Pronounced “Sassy” it’s an acronym of “Secure Access Service Edge”. SASE was announced as a security framework in 2019 by Gartner to address and combine the functions of network and security solutions into a unified cloud native service.
According to Gartner, “SASE capabilities are delivered as a service based upon the identity of the entity, real-time context, enterprise security/compliance policies and continuous assessment of risk/trust throughout the sessions. Identities of entities can be associated with people, groups of people (branch offices), devices, applications, services, IoT systems or edge computing locations.”
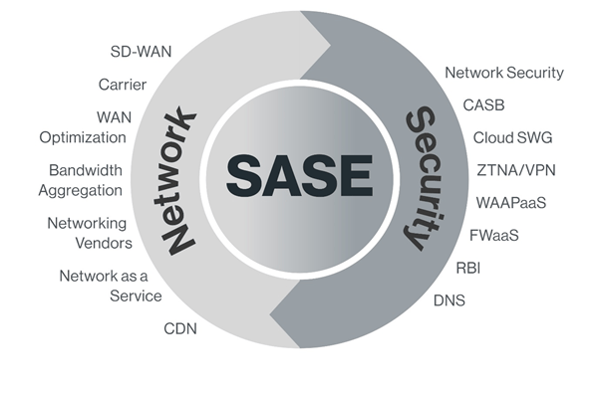
SASE is effectively a network framework that combines WAN capabilities with cloud-native security. Security services such as CASB, firewall as a service and the Zero Trust model, combined with the WAN functions that secure the experience and the session for the user when accessing cloud enabled applications, data and services anywhere, anytime.
SDWAN vs SASE
I can hear your thinking. Hey this sounds like an SDWAN solution.
SDWAN is a Software Defined Network (SDN) that utilises network overlay to connect branch offices to a central private network. Some cyber security vendors implement a Firewall in this network overlay and suddenly you have FWOS (Firewall as a Service). SDWAN is not built with the cloud in mind. It’s built with private networking in mind and offers all the benefits of SDWAN capabilities such as flexible bandwidth allocation, traffic prioritisation, traffic re-routing at the application level, and the list goes on.
SASE on the other hand has been architected with the remote user in mind with adoption of cloud computing in a distributed architecture. The remote user connects to a central network (gateway), where the Zero Trust model is utilised to access resources based in the cloud as well as any private networks, including SDWANs. With SASE, security services and networking functions are run in the cloud or a security pairing agent on the remote user’s device.
SDWAN is great to protect branch offices where it puts the private network in the centre of the network model. A SASE network is focused on providing cloud native security with the cloud and its resources at the centre of the network.
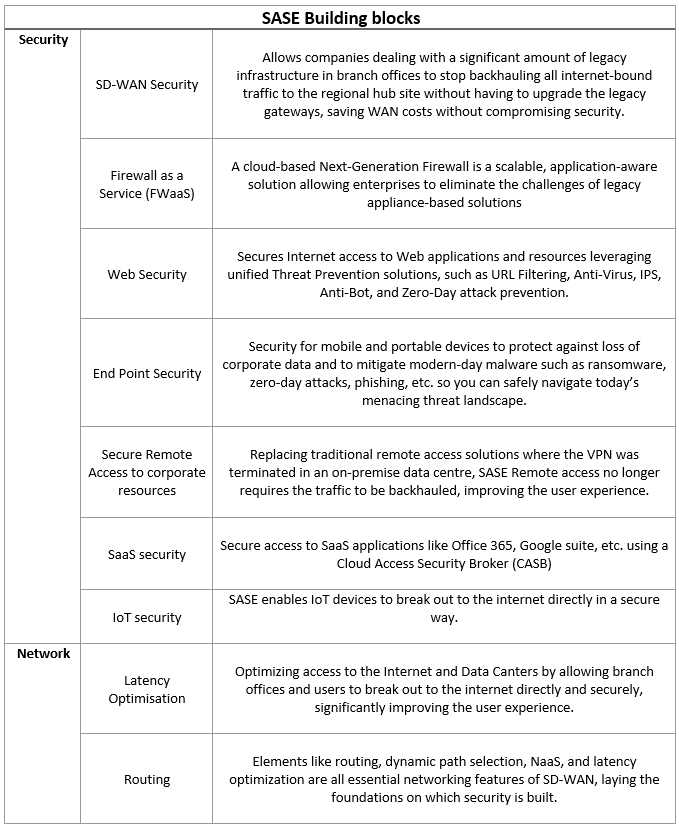
To offer SASE services you need to combine the networking and security into a single, cloud delivered offering. SASE models need to fulfil a number of requirements:
- The convergence of WAN edge and network security models
- Cloud-native, cloud-based service delivery
- A network designed for all edges
- Identity and network location
Conclusion
The adoption of cloud enabled applications for collaboration, storage and critical business core processes brings with it security challenges. Accessible anywhere at any time, this increases business productivity, but also increases the risk of security threats. As more organisations adopt cloud enabled processing launching an attack is even easier for malicious actors. Traditional security stacks and capabilities are failing to keep pace with the changing threat landscape; both from external and internal threats. It is imperative to have a security and risk management process in place. The SASE model combines the flexibility of the current networking models together with the cloud security capabilities focusing on remote users.

Meet the Team: Andy Taylor - DAS State Sales Manager

Federal Budget 2026–27: What It Means for SMB Technology Planning, Cybersecurity and Channel Partners

One HPE, One Opportunity: How Dicker Data Is Accelerating Partner Growth in 2026
Partner With Us
Our resellers outperform the competition and deliver next-level solutions for clients thanks to our unique, value-added services.
You May Also Like
These Related Stories

Tap into a growing demand for cloud security services with Dicker Data

VMware Think Series Part 1: How Standardized toolsets accelerate Cloud Migration
