We have all heard the great mantra that our people are our greatest asset but through a cyber security lens, is that necessarily true? In a social study, forty-eight percent of people said they would happily exchange their password for a piece of chocolate*. Diana Kelley, Cybersecurity Field CTO Microsoft explains that the new breed of cyber attackers' prey on our human nature in order to defraud. “...Small, very human actions have led to billions of dollars of loss to global business,” she says.
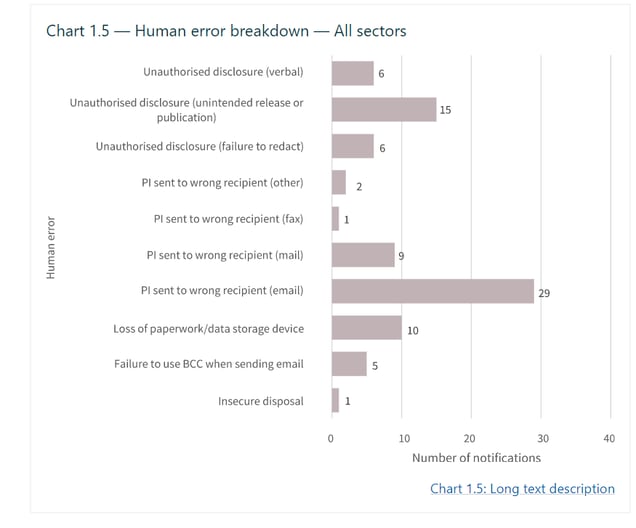
COVID, the recent government breaches and so many more factors mean that Security is top of mind for many businesses, SMB to large organisations. The natural starting point for these discussions sits with hardware and networks however it could all be for nought if processes and human-error are not taken into consideration. The National Data Breach is an amendment to the Privacy Act 1988 that mandates that mandates a reporting and notification process of eligible data breaches that occur on or after 22 February 2018 to the Office of the Australian Information Commissioner (OAIC). It’s reporting actually includes human-error as major category of risks to an organisation.
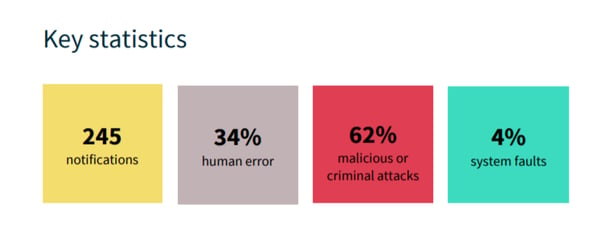
Looking at the report for Notifiable Data breaches in the August 2019 report it becomes apparent that from the 151 notifiable data breaches 84 were from human error.
Securing people is the practise of minimising risk to both the business and the staff themselves, in the role that they perform for your organisation.
It is important that we can clearly identify where the risks are and how we minimise those risks. This forms the foundation of any Security solution that businesses are trying to build. Whilst I do believe that we need to identify individual business requirements, we can have some guidelines on building the solution.
Here are my 3 top tips to consider about the human component of your Security systems:
- Audit: Conducting an audit that allows you to clearly identify the risks that exist in the network and what are you protecting. Consider, have you developed a holistic approach that takes into consideration the human element? How do we minimise the risk and develop the strategy moving forward?
- Keep it Simple: So often we think that to have a great solution we need to make it as complex as this will make it safer, however in this case, complexity is our enemy. By keeping the solution simple but still secure we achieve a better outcome for our users and our business. For example, a friend of mine was a lead guitarist in a famous 80s band everyone would comment on the guitar work, his reply was always ‘it’s a very simple tune just done to perfection’.
- Document & Communicate: Clearly outline what the policy and plan is with action that define the risks. You should also include the ways to minimise risk and the action your users take. It is important that we write policy like this in a manner that is clear concise and not in IT jargon. The simpler this can be communicated the better chance we have of getting a positive outcome.
The most valuable piece of the puzzle is your adoption plan. Have your users involved and active participants to your plan. Having an adoption plan is critical to not just the onboarding but your systems ultimate success.
Dicker Data Security Solutions
Dicker Data has partnered with industry leading security providers to ensure the Australian IT reseller community have access to a full suite of technology designed to fight cybercrime, protect data, reduce risk and organisation down time.
Our dedicated in-house software and security team work closely with our Australian IT reseller partners to understand their business requirements and deliver tailored, leading edge security solutions. Dicker Data's IT partners can leverage experience from our local team of sales, technical and product management specialists, as well as enjoy exciting, high value promotions and incentives.
*Trick with treat – Reciprocity increases the willingness to communicate personal data, Happ, Melzer, Steffgen, https://dl.acm.org/citation.cfm?id=2950731

Dicker Data Becomes First ANZ Distributor to Achieve Microsoft Frontier Status

Meet the Team: Andy Taylor - DAS State Sales Manager

Federal Budget 2026–27: What It Means for SMB Technology Planning, Cybersecurity and Channel Partners
Partner With Us
Our resellers outperform the competition and deliver next-level solutions for clients thanks to our unique, value-added services.
You May Also Like
These Related Stories

Aruba Instant On, or Aruba Instant: which one's right for you?

The time to strengthen your cybersecurity Go-To-Market strategy is now
