Secure your everything: a guide to layered security
What is Multi-Layer Security?
Multi Layered security – also known as "multi-level security" or "defence in depth", is a concept of protecting multiple threat vectors through multiple layers of security. Whether this is done at the application layer, network layer, physical layer, or any other layer; all layers possess entry points for malicious activity. Protection and prevention across all the layers decrease the risk of a cyber-attack, or malicious activity.
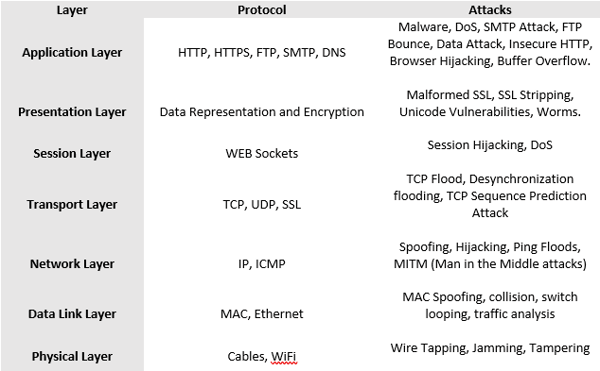
The standard network communication structure via the OSI layers is still present and all layers in the OSI 7 layer model possess possible security breaches.
See table below for layers of security and threat vectors.
Challenges of Multi-Layer Security
It’s a challenge for organisations to maintain multi-layered security defences for many reasons. What confuses this challenge is that the techniques and attack vectors that cybercriminals depend on are continually advancing. Many breaches occur through human error or businesses not investing in up to date or complete security solutions protecting the business. This means the threats such as ransomware and phishing impacting the business is very high.
The biggest challenge with a multi-layered security strategy is to deploy the right solutions at the right levels, using the most effective products, whilst keeping the economic expense and ongoing monitoring and maintenance to a cost effective and achievable level. Not only does technology play a role in preventing breaches, but the human factor is a considerable one. Phishing and identity theft breaches cost individuals and organisations immensely financially as well as their reputation.
Advantages of Layered Security
There is a distinct advantage of implementing your security posture across multiple layers. There is a need for security to extend to both the network and the software layer whether it’s bought off the shelf or developed in house. With each layer of security that is implemented, there is less and less access making it more difficult to infiltrate the system. Each layer running individually is not enough to cover most threat vectors. A combined set of layered security defences strengthens the defence and enforces a resilient defence system.
How does Multi-Layered Security Work
The multiple layers of security ensure that the defence component protects the data at that layer of any failure or loophole in the system. In a multi-layered security strategy, every layer focuses on key areas of security to prevent breaches. Each individual layer in the multi-layered security strategy focus on areas that are vulnerable to cyberattacks at that level.
The common types of solutions across security layers include:
- Application Protection
- Endpoint Protection
- Identity Management
- Patch Management
- Perimeter Security (Firewalls)
- Email and Web Filtering
- Data/Disk Encryption
- MFA
- Encrypted VPN
- DLP
Improving your Layered Security
There is no single silver bullet to provide complete protection across all layers. A combination of various solutions at various layers is required to minimise the risk. Each individual organisation will have a different requirement to the next organisation. Protecting the layers comes down to implementing not only defences at the various layers with technology, but the human factor also needs to be taken into consideration. Education and influences around procedures and best practices is recommended in any organisation.
- System Level Security
- Ensuring endpoints are properly configured to avoid many common security vulnerabilities and reduce the likelihood of a system-wide attack. Restrict Administrative Privileges, Strong Passwords, Data Encryption, patched systems, up to date firmware, etc
- Network Level Security
- Protecting internal network resources relies on several different methods, especially if employees are connecting remotely. Effective network-level security incorporates firewalls and intrusion detection and prevention systems, as well as packet inspection, web content filtering and HTTPS Inspection. Encrypted Remote Access through secure IPSEC or SSL VPN’s with MFA and/or digital certificates is also recommended for an enhanced Remote Access Security solution.
- Application Level Security
- Protecting critical software and applications from malicious attacks is an essential part of a layered security strategy. Poor application layer security can lead to performance and data theft. DDoS and other flooding techniques can cause considerable disruption from buffer overflows leaving systems exposed or unusable.
- Device Level Security
- Comprehensive Endpoint security solutions. Endpoint hardening is one of the most effective means of protecting a network from known software vulnerabilities and malware attacks. Up to date Endpoint Security solution with restrictions to detachable storage and unnecessary protocols, applications and ports.
- Human Factor
- Education and Best Practice with Security Awareness sessions with your staff is a great starting point. A solid Security Awareness policy and education session can help the staff understand the implications of a data breach or a cyber threat. Phishing attacks, and Data Leakage can be avoided.
- Design Business Policies around procedures, limitations, Organisation goals and most of all a clear set of controls designed to prevent and protect.
Conclusion
Any organisation is susceptible to cyber-attack, regardless of its size, location, operational model and sector.
There is no escaping the fact that cyber security threats will remain part of modern business, and the risks associated with this need to be managed moving into the future.
A multi-layered security approach should be made an important element of the overall IT security strategy in every organisation.
“Secure your Everything”. 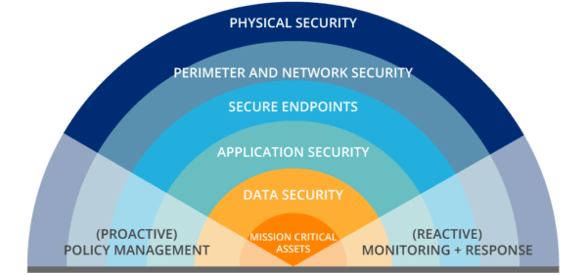

Meet the Team: Andy Taylor - DAS State Sales Manager

Federal Budget 2026–27: What It Means for SMB Technology Planning, Cybersecurity and Channel Partners

One HPE, One Opportunity: How Dicker Data Is Accelerating Partner Growth in 2026
Partner With Us
Our resellers outperform the competition and deliver next-level solutions for clients thanks to our unique, value-added services.
You May Also Like
These Related Stories

Trends driving endpoint security demand in a Work from Anywhere environment

Your Cyber Security Health Assessment
