5 Key Steps to Implementing a Zero Trust Security Strategy
While quite a pessimistic term, in the security world Zero Trust encourages the organisation to look at their systems more holistically and take a tough stance on data coming in regardless if it’s internal or external. The core tenant of Zero Trust is, as the name suggests ‘trust no one’ and has been developed to combat the more sophisticated cyber threats.
Zero Trust represents the next step from traditional castle-moat approach whereby businesses focus on securing perimeters. This method isn’t simply focused on keeping the bad stuff out, it also investigates what is roaming freely within our network as well.
“The strategy around Zero Trust boils down to don’t trust anyone. We’re talking about, ‘Let’s cut off all access until the network knows who you are. Don’t allow access to IP addresses, machines, etc. until you know who that user is and whether they’re authorized,’” explains Charlie Gero, CTO of Enterprise and Advanced Projects Group at Akamai Technologies in Cambridge, Mass.
Implementing Zero Trust
‘How do I transition to this new way and what do I need to do?’ I hear you ask; if you are asking the question, then you’re on your way, as defining what a Zero Trust approach looks like for your business is the first step.
5 key processes every business looking to implement Zero Trust should be following:
- Define Zero Trust for your business: It is important to sit down and discuss what Zero Trust means to you and how will it look in your organisation. At this point, it’s not necessary to get hung up on the technology, it is about the commitment to look at things differently and what change that can bring. The commitment to make it happen is key.
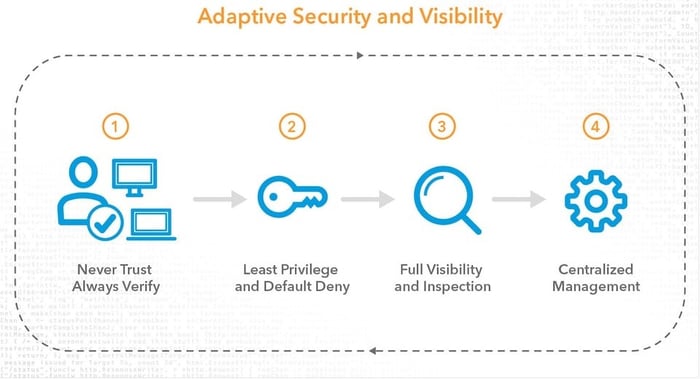
- Consider the End User: The Zero Trust approach of never trusting and always verifying can change how users interact with your systems and data. You need to know who your users are, what apps they are accessing how they are connecting to your apps and the controls you have in place for securing that access. I like to think about a clear focus on the user experience whilst considering what are you willing to trade off for security.
- Design your Process: It’s a bit like the schoolteacher that says ‘there is no wrong answer’… The great part of this exercise is that there is no single one approach for the implementation, Zero Trust is about protecting your applications by ensuring that only securely authenticated users and devices have access to them. Where you are on the network matters less than how well authenticated you are and how trustworthy your device is.
- Implement: Put your theory into practise and make the necessary changes to your systems which may include enhancing user passwords with multifactor authentication (MFA) and additional verification steps to determine the level of access to be granted for each user. Remember; Zero Trust principles need to apply regardless of user type—end user, privileged user, outsourced IT, partner or customer—or the resource being accessed. Your access decisions need to be adaptive and dynamic.
- Plan for the Challenges: We know that with any change comes challenges. This is a great time to think about how you will address the challenges when they come and the process to seeing them resolved. The ideal state being achieving a balance that allows the user to work productively, safely, anywhere.
Dicker Data Security Solutions
Dicker Data partners with industry leading security vendors to ensure the Australian IT reseller community have access to a full suite of technology designed to fight cybercrime, protect data, reduce risk and organisation down time.
Our dedicated team work closely with our Australian IT reseller partners to understand the business requirements of their customers and deliver tailored, leading-edge security solutions. Dicker Data IT partners can leverage the experience from our local team of sales, technical and product management specialists, as well as leverage promotions and incentives.

Meet the Team: Andy Taylor - DAS State Sales Manager

Federal Budget 2026–27: What It Means for SMB Technology Planning, Cybersecurity and Channel Partners

One HPE, One Opportunity: How Dicker Data Is Accelerating Partner Growth in 2026
Partner With Us
Our resellers outperform the competition and deliver next-level solutions for clients thanks to our unique, value-added services.
You May Also Like
These Related Stories

The benefits of Tape Data Storage in 2024 with HPE StoreEver LTO Tapes
Staging: Servers & Storage
