As the threat landscape continues to evolve, and industries transition from remote to hybrid work, security continues to be one of the top challenges of our digital age. Today, anything less than comprehensive security is no security at all.
Bringing together Dicker Data expertise with Microsoft resources, explore these guides to help you ensure your Microsoft cloud deployments are secure, cost-efficient, and set your SMB customers up for ongoing success!
Watch our fireside chat hosted by Darren Bennett
CSP Security Best Practices:
Where do your responsibilities to your customers start and end?
How do you safeguard your own business and reputation?
What is Microsoft doing to support you?
The Partner's Role:
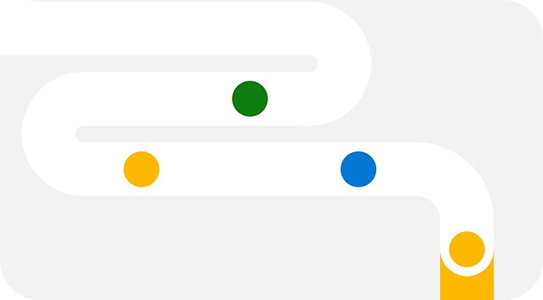
The Shared Responsibility Model (see graph) is a security & compliance framework that outlines the responsibilities of partners, cloud providers, and customers in cloud deployments. This model covers every aspect of the cloud environment, including hardware, infrastructure, endpoints, data, configurations, settings, operating system (OS), network controls and access rights.
Workload responsibilities vary depending on whether the workload is hosted on Software as a Service (SaaS), Platform as a Service (PaaS), Infrastructure as a Service (IaaS), or in an on-premises datacenter.
Useful Resources:
- For Partners:
- Share with Customers:

OnDemand Partner Enablement from Dicker Data
Re-watch or explore popular training sessions run by Dicker Data on various aspects of the Microsoft Security stack. Don't miss our most popular sessions the 'Microsoft Security Labs' which through a technical lens examine Zero Trust, Intune, Defender, and more.
Microsoft & Essential 8:
While no single mitigation strategy is guaranteed to prevent cyber security incidents, organisations are recommended to implement eight essential mitigation strategies as a baseline. This baseline, known as the Essential Eight, makes it much harder for adversaries to compromise systems.


Ebook: How a Consolidated Security Stack can Reduce Risk & Cost
As businesses pivot around post-COVID security strategies, it's a good time to revisit ways to streamline and strengthen security environments. Rather than cobbling together individual point solutions, consider a more integrated approach that providers comprehensive protection and enhanced capabilities.




One Pager: Phishing
Phishing is a form of fraud in which an attacker masquerades as a reputable person or company. Phishing attacks are popular with cybercriminals because it is easier to trick someone into clicking a malicious link than to break through a computer's defences. In this short brochure, you'll learn about Phishing basics and how Microsoft 365 Business Premium can detect and protect SMBs.
Frequently Asked Questions
Microsoft follows a shared responsibility model where you would be responsible for some aspects of security along with Microsoft and the customer. Responsibility varies by the type of workload i.e., IAAS, PAAS, and SAAS, you can find an infographic demonstrating the breakdown here.
The security solution you choose to implement for your customer should reflect the customer's unique needs and any compliance requirements however, at the very least we recommend turning on Multifactor Authentication (MFA) for all the users and following the Zero Trust guidelines. Here is the reference for you to get started.
MFA is considered a security default by Microsoft. Security defaults are free for every customer in Azure Active Directory Premium P1 & P2, and relevant M365 licenses.
In the past, as an organisation, you may have focused your defences on protecting network access with on-premises firewalls and VPNs, assuming that everything inside the network was safe. Today, as data footprints have expanded to sit off-premises in the Cloud, or across hybrid networks, the Zero Trust security model has evolved to address a more holistic set of attack vectors. Read more here.
Contact the Microsoft team at Dicker Data here. We have a team of experts across product, sales, and technical support who are available to walk through specific queries.
Microsoft Azure has many global regions. You can search the available geographies, here.
Regardless of the size of the environment, we recommended following Microsoft's best practices for your customers.
This can be achieved by using RBAC and following the principle of least privilege. For more information on the type of roles available please explore here.
Azure AD provides a sign-in activity report that can be utilized to check any malicious login attempts to the service. These logs can be further analysed by ingesting the data in log analytics/Microsoft Sentinel.
Various compliance standards such as CIS, and ISO2700 provide detailed instructions around security best practices. Microsoft Azure security benchmark can be used as a reference to implement various security controls for Azure. You can read more here.